18 Oct Peregrinate Increases Security for Confidential Emails
In order to protect emails containing private, sensitive, or confidential information Peregrinate now offer a secure encrypted email provision using private@secure-peregrinate.uk
Here is How it Works
Secure emails are encrypted using the current highest levels of encryption and are therefore 100% secure. Peregrinate have further invested in security in the form of a Virtual Private Network (VPN). All secure emails will have the additional security of being sent using a secure VPN link. We believe this provides the ultimate protection for sensitive correspondence.
Before sending encrypted emails, we will send you an encryption key (password) in a separate email which will allow you to open and read the contents of the encrypted email.
You will then receive a second email advising that you have an encrypted mail. Please click on the View Secure Message box in order to read the encrypted email as below.
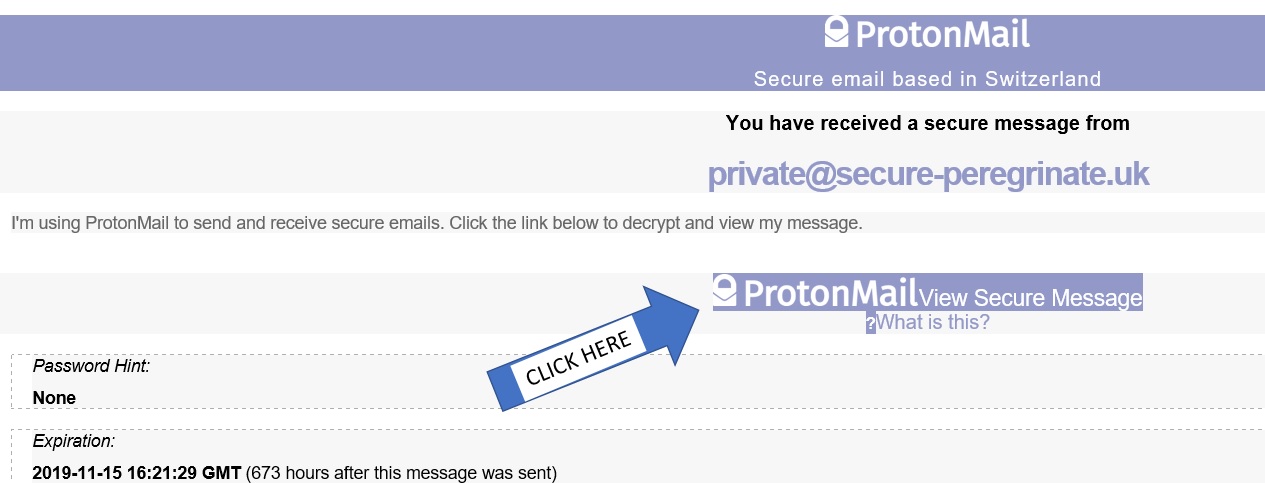
The encryption key will change for each sensitive email to provide further security. Please do not pass this key to anyone.
Once you have clicked View Secure Message you will be taken to our secure domain private@secure-peregrinate.uk. This is where you enter the encryption key as below.

The email will now be decrypted. You will note on the email page that the email will automatically delete 28 days after being sent. Should you require backup of the documents you should save them to your own secure site. You will be able to send a secure reply by clicking on the Reply Securely box. On the reply page at the bottom right, next to the send button you can add attachments if required. These will also be encrypted.

Private@secure-peregrinate.uk is live now. Please use this address for future confidential emails.
Peregrinate is committed to providing the highest levels of service across our whole provision. We trust this additional enhancement meets with your approval.
Just How Secure is private@secure-peregrinate.uk?
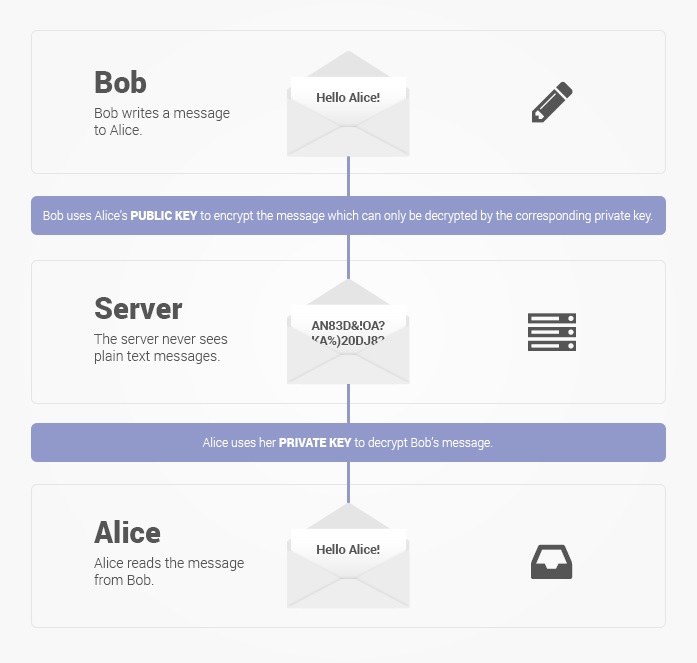
End-to-End Encryption
Messages are encrypted at all times
Messages are stored on ProtonMail servers in encrypted format. They are also transmitted in encrypted format between their servers and user devices. Messages between ProtonMail users are also transmitted in encrypted form within their secure server network. Because data is encrypted at all steps, the risk of message interception is largely eliminated.
Zero Access to User Data
Your encrypted data is not accessible to ProtonMail.
ProtonMail’s zero access architecture means that your data is encrypted in a way that makes it inaccessible to them. Data is encrypted on the Peregrinate side using an encryption key that ProtonMail do not have access to. This means they don’t have the technical ability to decrypt your messages, and as a result, they are unable to hand your data over to third parties. With ProtonMail, privacy isn’t just a promise, it is mathematically ensured. For this reason, ProtonMail are also unable to do data recovery. If you forget your password, we cannot recover your data.
Open Source Cryptography
Time-tested and trusted encryption algorithms
ProtonMail use only secure implementations of AES, RSA, along with OpenPGP. Furthermore, all of the cryptographic libraries they use are open source. By using open source libraries, we can guarantee that the encryption algorithms they are using do not have clandestinely built in back doors. Proton Mail’s open source software has been thoroughly vetted by security experts from around the world to ensure the highest levels of protection.
Additional Security with a Virtual Private Network (VPN)
Peregrinate have chosen to partner with Express VPN who encrypts our traffic between secure VPN servers and your computer, so that it can’t be read by third parties in between, such as your internet service provider or your local Wi-Fi operator.

Express VPN Advanced Encryption Standard
ExpressVPN uses AES (Advanced Encryption Standard) with 256-bit keys — also known as AES-256. It’s the same encryption standard adopted by the U.S. government and used by security experts worldwide to protect classified information.
A brute-force attack on a 256-bit keyspace is simply infeasible, even if all the world’s most powerful supercomputers ran for as long as the universe has existed so far, billions and billions of times over.